Advances in Biometrics Research in the Area of Facial Recognition
A few days ago, I had to make a call to my new insurance company. It was my first time calling them, and after a short period on hold I predictably found myself acting out a rather familiar scene: “Yes, I am still on the line … My name is Ioannis Kakadiaris … Yes, I can spell that for you: I-O-A-N, yes, N as in Nancy, N, no, two Ns, -I-S … Last name is spelled K-A-K-A, yes, K-A twice, I repeated it on purpose… “ I will spare you all the details of the exchange; suffice it to say that it reinforced my conviction that there ought to be a better way to identify and authenticate oneself, especially for those of us who are not named John Smith.
 What do I mean? Authentication (from the Greek αὐθεντικός, meaning "real, genuine”)
is the act of confirming the truth of an attribute of a datum claimed to be true by
an entity, much like when I am on the phone with my insurance company, claiming to
be the person called Ioannis Kakadiaris. There are several methods for authentication:
it can be something that only the person to be authenticated knows (e.g., my password),
or something that only the person to be authenticated has (a token, such as the key
for my house lock). But, it can also be something that the person is, one of their
physical attributes – that is to say, a biometric signature. And the biometric signature most of us use multiple times every day, much more often
than our name, is our face. Face recognition is about the promise of using our face
as a password.
What do I mean? Authentication (from the Greek αὐθεντικός, meaning "real, genuine”)
is the act of confirming the truth of an attribute of a datum claimed to be true by
an entity, much like when I am on the phone with my insurance company, claiming to
be the person called Ioannis Kakadiaris. There are several methods for authentication:
it can be something that only the person to be authenticated knows (e.g., my password),
or something that only the person to be authenticated has (a token, such as the key
for my house lock). But, it can also be something that the person is, one of their
physical attributes – that is to say, a biometric signature. And the biometric signature most of us use multiple times every day, much more often
than our name, is our face. Face recognition is about the promise of using our face
as a password.
In 1964, Bledsoe, Chan, and Bisson pioneered the development of the first face recognition system. Specifically, a human marked the coordinates of a set of landmarks (e.g., the center of pupils, the inside corner of eyes) in photographs, which were then converted to distances and used to recognize individuals. In 1973, the first automated face recognition system was presented in the Ph.D. thesis of Prof. Takeo Kanade. Since then, research in Face Recognition has received widespread attention due to its many applications. Nowadays, face detection is used by our smart phones to ensure better pictures of individuals, and face recognition is used by both Facebook and Google Picasa to effortlessly tag individuals in our photo collections.
 In 2004, the Biometrics cluster of my lab (Computational Biomedicine Lab, www.cbl.uh.edu) initiated research in the areas of face recognition. We pioneered the use of three-dimensional
data for face recognition and developed novel algorithms for face (and ear) recognition
when both the data in the gallery and the probe are three-dimensional. Our 3D-3D face
recognition software ranked first in the 3D-shape section of the 2007 Face Recognition
Vendor Test (FRVT) organized by National Institute of Standards and Technology (NIST).
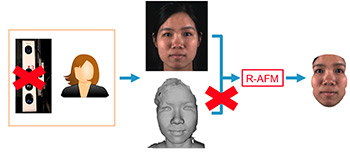
In 2010, we created a new research area called 3D-2D face recognition in which the
data in the gallery are three-dimensional (imagine that when you get your UH ID, 3D
data are acquired) while the probe data (a picture of my profile so I can enter the
parking lot) is two-dimensional. Our 3D-2D method outperforms the state-of-the-art
2D face recognition methods by addressing critical challenges in low resolution data,
accurate landmark localization, variations of indoor illumination, cross-resolution
matching, and score normalization. This development required developing novel methods
for: (i) data representations by learning the basis, representation, and metric simultaneously;
(ii) classifying imbalanced datasets; and (iii) sparse representations for missing
and incomplete data. In 2014, we began bringing to bear all our experience using three-dimensional
data by developing a novel method for extracting a three-dimensional face model from
a single image. Currently, we are focusing on refining that method, addressing challenges
of outdoor illumination and face recognition based on videos.
In 2004, the Biometrics cluster of my lab (Computational Biomedicine Lab, www.cbl.uh.edu) initiated research in the areas of face recognition. We pioneered the use of three-dimensional
data for face recognition and developed novel algorithms for face (and ear) recognition
when both the data in the gallery and the probe are three-dimensional. Our 3D-3D face
recognition software ranked first in the 3D-shape section of the 2007 Face Recognition
Vendor Test (FRVT) organized by National Institute of Standards and Technology (NIST).
In 2010, we created a new research area called 3D-2D face recognition in which the
data in the gallery are three-dimensional (imagine that when you get your UH ID, 3D
data are acquired) while the probe data (a picture of my profile so I can enter the
parking lot) is two-dimensional. Our 3D-2D method outperforms the state-of-the-art
2D face recognition methods by addressing critical challenges in low resolution data,
accurate landmark localization, variations of indoor illumination, cross-resolution
matching, and score normalization. This development required developing novel methods
for: (i) data representations by learning the basis, representation, and metric simultaneously;
(ii) classifying imbalanced datasets; and (iii) sparse representations for missing
and incomplete data. In 2014, we began bringing to bear all our experience using three-dimensional
data by developing a novel method for extracting a three-dimensional face model from
a single image. Currently, we are focusing on refining that method, addressing challenges
of outdoor illumination and face recognition based on videos.
As we move forward, overcoming the research challenges of pose, illumination, expression, and aging, researchers are cognizant of the need for privacy and respect of the Fourth Amendment of the U.S. Constitution. Keeping that in mind, we are about to witness an explosion of using face recognition to make our life easier using mobile technologies and multiple biometric traits to realize the vision of gaining access by using our face as the password.
- Ioannis A. Kakadiaris, Computer Science Department
This article originally appeared in the Winter 2015/2016 issue of the CS Now! Newsletter.